Executing a seven-figure trade on a standard retail exchange isn’t just inefficient; it’s a strategic mistake that can cost you thousands in slippage. While retail platforms serve the casual trader, high-net-worth investors require a more sophisticated approach to liquidity. If you’re wondering how to safely buy large amount of bitcoin in 2026, you’ve likely already hit the wall of low daily limits or the fear of exchange hacks during lengthy deposit holds. You understand that protecting your capital requires moving beyond public order books into the world of regulated OTC desks.
This guide will help you master the professional strategies used by global entities to acquire significant holdings without disrupting the market. We’ll show you how to secure a fixed, transparent price while ensuring 100% compliance with MSB and AML regulations. By the end of this article, you’ll know exactly how to leverage institutional-grade storage and T+0 settlement to move your assets from purchase to secure custody instantly. We’re bridging the gap between disruptive innovation and institutional reliability to ensure your transition into the future of payments is seamless and secure.
Key Takeaways
- Eliminate price slippage and avoid bot-driven front-running by shifting high-volume acquisitions from public order books to private liquidity pools.
- Discover how to safely buy large amount of bitcoin by utilizing regulated OTC desks that provide fixed, transparent pricing and superior transaction privacy.
- Verify institutional safety by confirming your provider holds MSB registrations in the US and Canada to ensure full compliance with global AML standards.
- Implement a professional execution framework that prioritizes institutional-grade cold storage and instant T+0 settlement for immediate asset security.
- Partner with a global enabler to bridge the gap between traditional finance and the future of payments through seamless, high-liquidity crypto-fiat conversions.
The Challenge of Scale: Why Retail Exchanges Fail Large Buyers
High-volume traders often realize too late that retail platforms aren’t built for scale. While a standard exchange app works for a thousand-dollar purchase, it’s a liability for seven-figure entries. If you’re researching how to safely buy large amount of bitcoin, you must first understand the structural limitations of public order books. Retail platforms rely on “instant buys” that prioritize convenience over price efficiency, whereas institutional acquisition requires professional liquidity provision.
The most immediate hurdle is slippage. This is the difference between the expected price of a trade and the price at which the trade actually executes. In low-liquidity environments, a large buy order eats through the available “sell” offers at the current price and begins filling at progressively higher levels. You don’t just pay the market rate; you drive the market rate up against yourself. Public order books also signal your intent to the entire market. High-frequency trading bots detect large incoming orders instantly, “front-running” your trade by buying up the supply and selling it back to you at a premium.
Beyond price execution, the “withdrawal trap” remains a significant operational risk. Retail exchanges often freeze large sums for weeks under the guise of “manual review” or compliance checks. While these platforms are quick to accept your deposit, moving a significant amount of capital out to private custody can become a bureaucratic nightmare. This friction is exactly why sophisticated investors choose off-ramp solutions and OTC desks that prioritize settlement speed and regulatory clarity.
Understanding Liquidity Gaps
A $1,000,000 buy order on a standard retail platform can move the market price by 2% to 3% in seconds. Deep liquidity is the only defense against market volatility during execution. Many “zero-fee” platforms hide their real costs within a massive spread; you aren’t paying a commission, but you’re buying at a price significantly higher than the global average. True institutional liquidity ensures that your entry doesn’t create an artificial price spike.
The Risk of Centralised Custody
Leaving large holdings on a standard exchange creates a single point of failure. To understand what is Bitcoin is to recognize it as a decentralized asset that requires sovereign control. We recommend transitioning assets to immediate self-custody or multi-sig solutions as part of a robust crypto security strategy for large holdings. The goal is to move from the exchange to a secure wallet as fast as the network allows, ensuring your assets aren’t vulnerable to platform insolvency or internal security breaches.
OTC Desks vs. Traditional Exchanges: Which is Safer?
Over-the-Counter (OTC) trading represents the professional standard for high-volume digital asset acquisition. Unlike the public order books discussed previously, an OTC desk facilitates a private, direct transaction between two parties. For investors determining how to safely buy large amount of bitcoin, this model eliminates the visibility that typically triggers market volatility. Your trade doesn’t appear on public exchange tickers; it’s a discrete settlement that protects your strategy from prying eyes and competitive front-running.
The primary safety feature of an OTC desk is the fixed-price model. On a standard exchange, you’re at the mercy of a shifting spread during the time it takes to fill a large order. With a professional desk, you receive a locked-in quote before you hit confirm. You know your exact entry price and the total fiat commitment required, removing the guesswork from your capital allocation. While retail guides on how to buy Bitcoin focus on small-scale entries, institutional OTC desks operate on an entirely different plane of execution, prioritizing price certainty over simple interface convenience.
Personalised Trade Execution
Institutional desks provide a level of service that retail platforms can’t match. You’re assigned a dedicated account manager who oversees your transaction from the initial quote to final settlement. These professionals source liquidity from multiple private pools simultaneously, ensuring your trade executes at a stable price even during periods of high market stress. The speed of execution is equally impressive; you can move from fiat to BTC in minutes. This efficiency is a hallmark of the future of payments, where high-value settlements happen in real-time without the multi-day delays common in traditional finance.
Physical vs. Digital OTC
Trust is the foundation of any large-scale financial operation. While digital OTC desks are efficient, visiting a physical office in a global financial hub provides an extra layer of security for high-net-worth individuals. Physical desks allow for face-to-face verification of the service provider’s credentials and security protocols. For those prioritizing physical security, buying bitcoin with cash at a regulated office provides a tangible layer of trust that digital-only platforms can’t replicate. These locations follow strict in-person security protocols to ensure that high-volume exchanges remain confidential and secure. If you’re ready to experience this white-glove service, exploring our off-ramp solutions can provide the professional bridge you need for secure capital movement.

Compliance Checklist: Verifying Your Provider’s Safety
Safety in high-volume transactions isn’t just about the technology; it’s about the regulatory foundation of the provider. When you’re determining how to safely buy large amount of bitcoin, the provider’s legal standing is your first line of defense. A sophisticated investor knows that a firm’s registration status is the most reliable indicator of its financial integrity and operational stability. It’s the difference between a secure institutional partner and a high-risk platform that could fail under regulatory pressure.
In the US and Canada, a Money Service Business (MSB) registration is a mandatory requirement for any entity handling significant digital asset volumes. This isn’t just a local permit. It’s a signal that the entity is subject to federal oversight and rigorous financial auditing. Many retail traders view KYC and AML protocols as hurdles, but for institutional investors, they’re essential safety features. These protocols prevent your capital from being commingled with illicit funds, protecting you from future legal or banking complications. Using a provider that offers integrated fiat settlement ensures a clean, bank-grade transaction trail, which is vital for corporate accounting and tax reporting in 2026.
Regulatory Red Flags
Spotting “ghost” exchanges is critical for capital preservation. If a platform lacks a physical global footprint or a verifiable registration, it’s a major risk. Large-scale “no-KYC” offers are often a trap; they attract regulatory scrutiny that could lead to your funds being seized during a review by banking partners. Transparent fee structures are also a hallmark of institutional quality. If the fees are buried deep within the spread, you aren’t dealing with a professional desk. A reliable partner will always provide a clear breakdown of costs before you commit any capital.
The MSB Advantage
MSB registration ensures a company is audited for financial integrity and maintains strict operational standards. Institutional partners prefer otc crypto exchanges that hold multiple global licenses, as this demonstrates a commitment to long-term stability and cross-border compliance. You can verify these registrations yourself by checking the FinCEN registry in the US or the FINTRAC database in Canada. This verification step is a simple but powerful way to confirm you’re working with a legitimate global enabler rather than a fly-by-night operator. By choosing a registered entity, you ensure your trade is backed by a professional bridge that connects the old world of finance with the new.
Step-by-Step: Executing Your First Large Bitcoin Buy
Transitioning from the theoretical risks of retail exchanges to the practical execution of a high-volume trade requires a disciplined framework. Knowing how to safely buy large amount of bitcoin is a matter of following a professional protocol that prioritizes asset security and price certainty. This step-by-step process ensures your transition into the future of payments is efficient, compliant, and secure. If you require high-volume liquidity, you must first secure your destination before initiating the capital move.
- Step 1: Secure institutional-grade storage. Establish a cold storage solution or a multi-sig setup to ensure you aren’t reliant on a third-party platform’s internal security.
- Step 2: Select a regulated OTC provider. Choose a partner with a global footprint and verified MSB status in jurisdictions like the US and Canada to guarantee financial integrity.
- Step 3: Complete Enhanced Due Diligence (EDD). Provide the necessary documentation to unlock institutional volume limits and satisfy 2026 AML requirements.
- Step 4: Request a quote and lock in your price. Obtain a fixed price to eliminate the risk of slippage that typically plagues public order books.
- Step 5: Execute the transfer and verify. Initiate the settlement and confirm the transaction on the blockchain to ensure the assets have reached your secure custody.
Preparing Your Wallet
Your destination must be as secure as your source. You should never use a retail exchange wallet for long-term large holdings because they represent a single point of failure. We recommend the “test transaction” rule: always send a small amount to verify the address before committing the full buy. Whitelisting these verified addresses on your platform adds a final layer of protection against unauthorized transfers. This simple step prevents catastrophic loss due to clerical errors or address-switching malware.
Settling the Transaction
Professional settlement options include bank transfers, wires, or cash-to-crypto moves at physical desks. For transactions exceeding $10,000, your provider will handle mandatory filings like Form 8300 to maintain your compliance trail. Understanding the off-ramp process is equally important; you need a clear strategy for when you eventually convert those assets back to fiat. After the trade, retain all documentation for tax purposes, as US brokers now report sales via Form 1099-DA. Ready to execute with institutional precision? Start your high-volume transaction with Pallapay today for instant, secure settlement.
The Pallapay Advantage: Global Institutional Liquidity
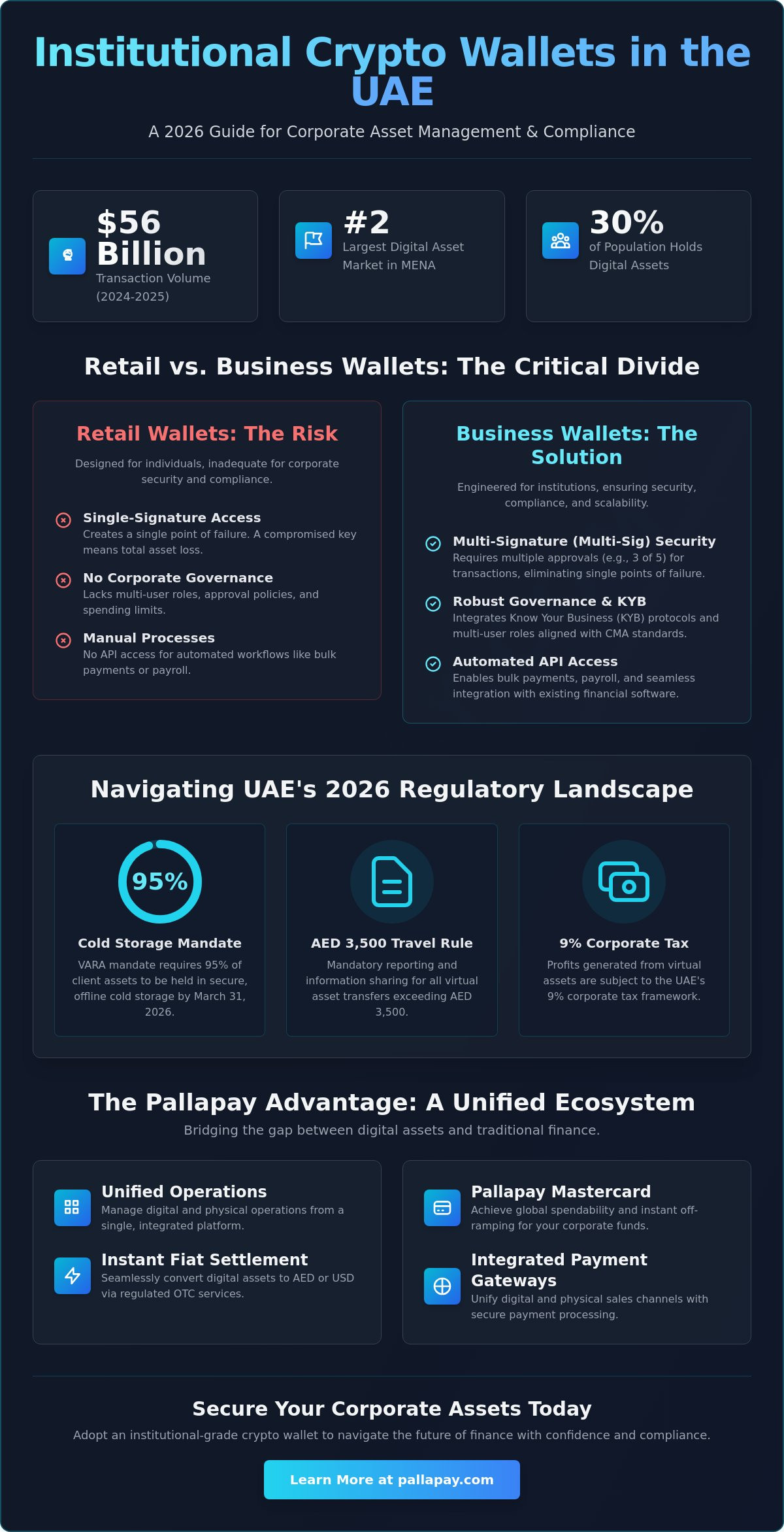
Pallapay serves as the definitive professional bridge between traditional capital and the digital economy. If you’ve been researching how to safely buy large amount of bitcoin, our ecosystem provides the regulatory certainty and deep liquidity required for significant acquisitions. We anchor our global operations on MSB registrations in the United States and Canada, creating a foundation of trust that retail platforms can’t match. This institutional alignment ensures that every high-volume transaction is backed by the same financial reliability you expect from a global fintech leader.
Unlike digital-only competitors, we maintain a robust network of physical OTC desks in strategic global hubs such as Singapore and Istanbul. This physical presence allows us to facilitate high-volume cash trades with a level of privacy and security that is unique to the Pallapay ecosystem. For privacy-conscious high-net-worth individuals, the ability to execute a face-to-face transaction at a regulated office provides an irreplaceable layer of physical trust. We bridge the gap between disruptive blockchain innovation and the practicalities of modern commerce, ensuring your move into digital assets is both secure and professional.
We eliminate the volatility risks discussed in previous chapters through our zero-slippage execution model. Every trade is Instant. By sourcing from a massive global liquidity pool, we ensure that your entry price is fixed and transparent, regardless of the order size. This efficiency reflects our role as a visionary partner in the future of payments, where high-value settlements happen in real-time without the friction of traditional banking delays.
Institutional Grade OTC
Our reach extends to 180+ countries, offering localized expertise that simplifies complex cross-border settlements. You gain access to a 24/7 global liquidity pool, ensuring that market hours never dictate your investment strategy. This all-in-one ecosystem doesn’t just stop at acquisition; it provides clear pathways for long-term utility. Once your position is secured, you can explore our comprehensive guide on how to spend cryptocurrency to integrate your holdings into your daily business operations or personal lifestyle.
Security and Compliance
Our commitment to institutional security is absolute. we employ the highest standards of AML and KYC to protect our clients from the risks of illicit capital commingling. This dedication is why global merchants and HNWIs consistently choose Pallapay for their most significant financial operations. We handle the heavy lifting of technology and compliance so you can focus on your portfolio’s growth. Contact our OTC desk today for a private consultation and experience the standard of institutional liquidity.
Secure Your Position in the Future of Payments
High-volume Bitcoin acquisition requires a shift from retail convenience to institutional precision. You’ve learned that avoiding public order books is essential to eliminate slippage and protect your entry price from market-signaling bots. By prioritizing providers with MSB registrations in the USA and Canada, you ensure your capital moves through a compliant, audited framework that meets the highest standards of financial integrity.
Understanding how to safely buy large amount of bitcoin is the foundation of a sophisticated digital asset strategy. Our global network of physical OTC desks and deep liquidity pools provide the Instant, zero-slippage execution necessary for your most significant trades. We handle the heavy lifting of compliance and technology so you can scale with confidence.
Securely execute your large Bitcoin trade with Pallapay OTC and partner with a global enabler dedicated to your financial stability. The transition to a digital-first economy is inevitable; make sure your entry is handled with the professional expertise it deserves.
Frequently Asked Questions
What is considered a “large” Bitcoin purchase in 2026?
A large purchase is generally defined by the minimum requirements of institutional OTC desks, which typically range from $50,000 to $100,000. In 2026, major global desks like Kraken or Bitget maintain a $100,000 minimum for private execution. These thresholds ensure the trade size is sufficient to access dedicated liquidity pools rather than public order books, providing the necessary depth for institutional entries.
How do I avoid slippage when buying $1 million worth of Bitcoin?
You avoid slippage by executing your trade through an Over-the-Counter (OTC) desk instead of a standard retail exchange. When you’re determining how to safely buy large amount of bitcoin, a professional desk provides a fixed price quote before you confirm the trade. This protects you from the 2% to 3% price spikes that often occur when large orders are filled on public platforms.
Is it safer to buy Bitcoin with cash or bank transfer for large amounts?
Both methods are secure when you use a registered Money Services Business (MSB). Bank transfers are preferred by corporate entities because they provide a transparent audit trail for accounting. However, buying with cash at a regulated physical office offers a unique layer of privacy and face-to-face security. The choice depends on whether you prioritize digital documentation or physical transaction privacy.
Why do I need to go through KYC for high-volume trades?
KYC is a mandatory safety protocol that ensures your transaction complies with global Anti-Money Laundering (AML) standards. For high-volume traders, this process is an essential layer of protection that ensures the provider’s liquidity is verified and clean. It also allows you to unlock institutional volume limits and establishes a professional relationship that’s necessary for secure, large-scale financial operations.
Can I buy large amounts of Bitcoin instantly?
Yes, you can execute significant trades instantly through providers that offer T+0 settlement. While retail platforms often impose low daily limits or freeze large withdrawals for manual review, institutional OTC desks are designed for real-time liquidity. This instant settlement is a cornerstone of the future of payments, allowing you to convert fiat to digital assets without the multi-day delays common in traditional banking.
What is the best way to store millions of dollars in Bitcoin safely?
The gold standard for securing millions in Bitcoin is a non-custodial hardware wallet or a multi-signature (multi-sig) setup. These solutions keep your private keys offline and require multiple authorizations for any transaction, eliminating the risks associated with centralized exchange custody. Self-custody ensures you retain absolute control over your assets, protecting your holdings from platform insolvency or internal security breaches.
How do OTC desks handle price discovery for large orders?
OTC desks perform price discovery by aggregating liquidity from multiple private pools rather than relying on a single public exchange ticker. They provide a single, locked-in quote based on real-time global market depth. This aggregation allows you to execute a massive order at one fixed price, shielding your transaction from the volatility that typically follows large, visible trades on public order books.
What are the tax implications of a large Bitcoin acquisition?
Buying Bitcoin isn’t a taxable event, but you must maintain accurate records for future reporting. In 2026, US-based brokers report sales via Form 1099-DA, and any business receiving over $10,000 in crypto must file Form 8300. Knowing how to safely buy large amount of bitcoin includes securing a clear transaction trail to ensure your long-term capital gains are calculated correctly when you eventually exit.
Disclaimer
The information provided on this website and blog is for general informational and educational purposes only and does not constitute financial, investment, legal, tax, or other professional advice.
Cryptocurrency and digital asset services may be subject to regulatory restrictions in certain jurisdictions. Users are solely responsible for ensuring compliance with applicable local laws and regulations before using any products or services mentioned on this website.
PallaPay does not guarantee the accuracy, completeness, or timeliness of any information published and accepts no liability for any loss or damages arising from reliance on the content. Any opinions expressed are those of the respective authors and may change without notice.
Certain services, features, or products referenced may be provided through third-party partners, licensed entities, or affiliated service providers subject to separate terms and regulatory approvals. Availability of services may vary by country or region.
This website may contain references to digital assets, virtual currencies, or blockchain-related services that are not available to residents of certain jurisdictions, including where prohibited by law. Nothing on this website constitutes an offer, solicitation, or recommendation to buy or sell any financial instrument or virtual asset.